Company
Contact
Phone : +852 28510271
Fax. : +852 28510155
Email : [email protected]
Security Assessment is generally referring to a Vulnerability Assessment which scans an organization’s infrastructure and identifies vulnerabilities (faulty firewall, lack of system updates, malware, etc.). With the assessment results, the technician can recommend steps to remedy the problems within the system.
A penetration test, or sometimes pentest, is a software attack on a computer system that looks for security weaknesses, potentially gaining access to the computer’s features and data.
Vulnerability scanner is a computer program designed to assess computers, computer systems, networks or applications for weaknesses.
Policies should be reviewed at planned intervals to ensure their continuing suitability, adequacy, and effectiveness.
Source code scanning is to analyze source code and/or compiled version of code in order to help find security flaws. Ideally, such tools would automatically find security flaws with such a high degree of confidence that what’s found is indeed a flaw.
Security Awareness Training will educate employees about corporate policies and procedures for working with information technology (IT). Employees should receive information about who to contact if they discover a security threat and be taught that data as a valuable corporate asset.
To fight against day to day evolving potential threat, we provide multi layer network protection solution to help you to prevent unauthorized access to your corporate network. These solution combine the technologies include firewall, antivirus, instruction prevention system and safeguard your network access gateway.
For authorized remote access, we provide SSL VPN with two factor authentication solution. Such solution enables a secure and ease-to-use communication channel for your business partner to connect from remote network, home or even hotel.
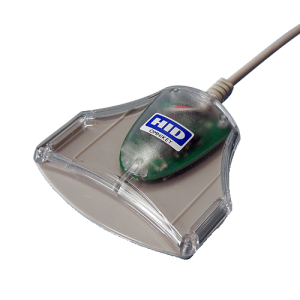
Physical security restricts access to company premises and logical security protects IT resources. These two areas usually work independently. Now organizations need to mitigate information theft risk and comply with data protection regulations. We provide an integrated approach to combine power of both physical security control and logically security control with one single employee card. Employee with on single card (with contact or contactless technology) can securely identify himself and access authorize physical and logical resources.
Data leakage may occur when data itself is being transferred, processed or even at rest. The increasing use of mobile devices and removable media make the chance of data leak increases substantially. To cope with the problem, we provide Data Leakage Prevention (DLP) solutions which include encryption, access control, device control and content filtering to help you to protect the data at rest, data in motion and data in processing.
What is RTTP?

Reindustrialisation and Technology Training Programme (RTTP) is a funding scheme under the Innovation and Technology Fund which subsidises local companies on a 2:1 matching basis to train their staff in advanced technologies, especially those related to “Industry 4.0”.
What is the funding ceiling?
Each company is subject to a funding ceiling of HK$500,000 in each financial year at the time of approving the application.
How to apply for a training grant?
Companies interested in applying for training grant for their employee(s) to attend registered public courses should apply via the online system (https://rttp.vtc.edu.hk) at least two weeks before the commencement of the courses. A list of registered public courses is available for reference. For tailor-made courses, companies should apply for course approval and training grants in one go.
RTTP Course
UDS is a qualified course provider under the Reindustrialisation and Technology Training Programme(RTTP). UDS supports RTTP Training Program by launching Security Awareness Training – Anti Phishing Workshop. For more detail of this course, please refer to workshop detail.
The objective of the workshop is to help candidates understand how phishing attacks work, the tactics that cyber criminals employ, how to spot and avoid a potential attack and most importantly you’ll be improving yourself and less vulnerable to phishing attacks.
UDS also provides other training related to cyber security in order to promote and encourage applicants to adopt lifelong learning in the manner of advanced technologies, especially those related to “Industry 4.0”.
UDS is found by a group of IT expertise. Our mission is to be a leading information security solutions provider with a high level of service commitment in the region.
UDS specializes in various IT Security Technologies, UTM Solutions, Network/Application Performance Monitoring Solutions, SOAR Architect and Implementation, IT Audit, and Security Assessments Services. In the past few years, we have provided many security solutions to Hong Kong Government Departments and enterprise customers.
In addition to our product offering, UDS also provides professional services including project management, customization, consultation, integration, solution design, implementation and training.
To be specialized in the Information Security field, and clouding services most of our technical staff have obtained industry-recognized information security certification such as CEH, CISA, CISM, CRISC, CDPSE, CBCP and CISSP with the Project Management Professional.
We understand IT security is a key to your business success. Our IT security consulting service is design to help you to minimize and mitigate the potential risk and vulnerability to your business and ensure your business operation is in a protected environment. Our security consulting services include:
- IT security requirement survey
- Architect the enterprise IT security infrastructure
- Feasibility study of IT security implementation
- Renew and update the security policy and guideline
- Provide security awareness education and training
Our system design and implementation services provide proven methodologies and best practices that accelerate the time to value of your project investment. Our project implementation services deliver on schedule, outstanding design, implementation, and integration services—in every engagement, in every location.
In addition to system implementation, we also provide profession training service to help customer to adopt the new technology and system rapidly.
A key benefit of working with UDS implementation team is the proven project management skill that is used along with skilled consultants to reduce risk and manage projects to on-time delivery within budget.
We provide 8×5, 7×24 onsite or remote support.
We offer security audit and assessment service to enable your business constantly meet the industry security best practice and your IT asset are well protected. Our aduit and assessment services include:
- IT system infrastructure review
- Internal security assessment test
- External security assessment test
- Renew security guides
- Renew the security policy setting in various device and system such as windows server, Unix server, firewall, VPN, Anti-Virus systems etc.
- Penetration Test, Vulnerability scanning, Security Policy Review, Source code scanning, Security awareness training
- Security Assessment is generally referring to a Vulnerability Assessment which scans an organization’s infrastructure and identifies vulnerabilities (faulty firewall, lack of system updates, malware, etc.). With the assessment results, the technician can recommend steps to remedy the problems within the system.
- A penetration test, or sometimes pentest, is a software attack on a computer system that looks for security weaknesses, potentially gaining access to the computer’s features and data
- vulnerability scanner is a computer program designed to assess computers, computer systems, networks or applications for weaknesses.
- Policies should be reviewed at planned intervals to ensure their continuing suitability, adequacy, and effectiveness.
- Source code scanning is to analyze source code and/or compiled version of code in order to help find security flaws. Ideally, such tools would automatically find security flaws with such a high degree of confidence that what’s found is indeed a flaw.
- Security Awareness Training will educate employees about corporate policies and procedures for working with information technology (IT). Employees should receive information about who to contact if they discover a security threat and be taught that data as a valuable corporate asset.